How Did Someone Use My Debit Card without Having It physically having it by obtaining the card’s number, CVV, and sometimes the PIN through various means such as data breaches, phishing scams, or skimming devices. With just this information, fraudsters can make unauthorized online purchases or even create duplicate cards. This type of fraud happens even if the cardholder never used their card in certain places or kept it safely stored.
Criminals use increasingly sophisticated methods to steal card details without direct access to the physical card. These methods include hacking into weak security systems, intercepting data during transactions, or tricking individuals into revealing sensitive information. Understanding how these techniques work is essential for recognizing risks and protecting one’s money from unauthorized use.
How Debit Card Fraud Happens Without Physical Access
Debit card fraud can occur even when the thief does not have the physical card. Criminals often obtain card details through various methods that bypass the need for the card’s presence or the PIN, taking advantage of vulnerabilities in digital transactions and human behavior.
Card-Not-Present Transactions
Card-not-present (CNP) fraud happens when someone uses stolen debit card information to make online or phone purchases. Hackers only need the card number, expiration date, and CVV code, which can be obtained through data leaks or skimming. No physical card or PIN is necessary since merchants often verify identity by matching billing details or sending one-time passwords.
This type of fraud can drain accounts quickly because it bypasses chip security features and PIN requirements. Contactless and electronic debit card transactions may be more vulnerable if the merchant’s system lacks strong authentication. It is essential for cardholders to monitor transactions closely and use card controls where available.
Digital Skimming and Data Breaches
Digital skimming involves criminals inserting malicious code into compromised websites or apps to capture card details during checkout. Large data breaches also expose millions of card records, including chip and magnetic stripe data, which can then be sold or used for fraud.
Chip malfunctions or weak encryption can sometimes allow fraudsters to clone card data electronically. An electronic debit card that relies on online systems may be subject to hacking, making timely software updates and security patches critical for issuers and merchants alike.
Phishing and Social Engineering Attacks
Phishing tricks victims into voluntarily providing sensitive debit card information. Fraudsters send emails, text messages, or phone calls pretending to be legitimate banks or companies, asking for card details, PINs, or passwords.
Social engineering exploits trust and urgency to bypass security. A user might share information due to fear of account suspension or promised rewards. Once the attacker has the card number and related data, they can make unauthorized purchases without the card or PIN. Awareness and verification of communication sources are key defenses.
Common Methods Used to Steal Debit Card Information
Criminals use several specific tactics to gain access to debit card details without physically possessing the card. These methods often target weak points in online systems, payment terminals, or user behavior to capture sensitive data like card numbers and PINs.
Online Database Breaches
Hackers frequently target large databases where merchants store debit card information. When a breach occurs, card data can leak onto underground forums or credit card dump sites, where it is bought and sold by criminals.
These breaches often affect businesses with weak cybersecurity, such as smaller companies or service providers. The stolen data may include the full card number, expiration date, and CVV codes, enabling unauthorized online purchases.
People who never shared their card details online can still be affected if their bank or a merchant they use suffers a breach. These incidents emphasize the need for monitoring account activity and using alerts for unusual transactions.
Skimming Devices at ATMs and Point of Sale
Skimming devices are hardware attachments criminals install on ATMs, gas pumps, or payment terminals. These devices secretly capture the magnetic stripe data when a card is swiped.
Some scammers go further by installing small cameras or keypad overlays to record PIN entries. The collected data allows them to clone cards or conduct online shopping with the stolen information.
Skimmers can be difficult to spot because they are designed to mimic the original machine parts. Users are advised to check for loose or unusual attachments on card slots and use trusted machines in well-lit locations.
Malware and Keyloggers
Malware installed on a victim’s computer or mobile device can capture debit card information when entered online. Keyloggers track every keystroke, including card numbers, usernames, and passwords.
This type of attack is common when users click on suspicious links or download infected files. The malware sends the recorded data to attackers without the user’s knowledge.
Financial apps and web browsers that lack proper security measures are more vulnerable. Regular software updates and using antivirus tools reduce the risk of malware attacks significantly.
Phishing Emails and Fraudulent Calls
Phishing schemes often involve fraudulent emails or phone calls claiming to be from banks or trusted companies. These attempts trick cardholders into revealing debit card details, PINs, or personal identification information.
The messages may create urgency, asking the victim to confirm suspicious transactions or reset passwords. Once the thief obtains this information, they can use it for online transactions or identity theft.
Recognizing legitimate communication from financial institutions is crucial. Cardholders should avoid clicking links in unsolicited emails and verify requests by contacting their bank directly using official phone numbers.
Signs of Unauthorized Debit Card Use
Unauthorized use of a debit card often reveals itself through specific signs. These include unfamiliar charges appearing on statements, unexpected alerts about transactions, or problems when trying to use the card.
Unexpected Transactions on Your Statement
One of the most obvious signs is seeing unfamiliar charges on your bank or credit card statement. For example, entries like 100 Deerfield Lane charge on debit card or Good Sportsman charge on credit card can indicate fraud. These may be small or large amounts, often from merchants you have never visited.
It’s important to carefully review your statement each month. Fraudulent charges may come from companies such as Acqra charge on credit card or Blossom Up charge on credit card. Promptly identifying and reporting these helps prevent further losses.
Receiving Alerts for Purchases You Didn’t Make
Many banks send push notifications or emails when a card is used. If you receive alerts for purchases you didn’t authorize, such as a Towson CMF charge credit card, this is a red flag.
These real-time alerts allow cardholders to act quickly. Not ignoring them can stop criminals from draining accounts and limit potential damage. If an alert seems suspicious, contacting the bank immediately is crucial.
Declined Payments and Account Lockouts
If a debit card is suddenly declined or your account gets locked without explanation, it may be because the bank flagged suspicious activity. This can happen after fraudulent charges are detected or reported.
Unexpected declines during usual transactions could mean someone else is trying to use the card data. Account lockouts are often precautionary but require contacting the bank to restore access and verify transactions. Monitoring these signs can help catch fraud early.
Immediate Steps to Take After Discovering Debit Card Fraud

When unauthorized transactions appear on a debit card, quick and precise action is critical. Promptly addressing the issue limits financial loss and protects the account from further compromise. Taking measured steps to communicate with the bank, secure the card, and dispute charges ensures better control over the situation.
Contacting Your Bank or Card Issuer
The first action is to contact the bank or card issuer immediately. Many banks provide a dedicated fraud hotline for these situations. Providing detailed information, including transaction dates and amounts, helps the bank understand the scope of the fraud.
If the card is a Visa debit or a standard US debit card, reporting the fraud quickly is equally important due to differences in protections and policies. Banks may offer provisional credits while they investigate.
Customers should have their account number, recent statements, and identification ready when calling. Reporting early not only helps recover funds but also starts the formal fraud investigation process.
Freezing or Canceling Your Card
Locking or freezing the debit card through the bank’s mobile app or online platform can immediately stop new transactions. If this option is unavailable, requesting a cancellation is necessary.
Freezing the card is a temporary hold that prevents new purchases but allows a cardholder to lift the hold if the card is found or transactions turn out to be valid. Canceling the card permanently deactivates it and triggers a reissue of a new card with a different number.
Both actions protect the account from continued unauthorized use. The new card will have new PINs and security codes, which should be kept secure and never shared.
Disputing Unauthorized Transactions
After reporting and securing the card, disputing fraudulent charges is the next step. Banks require a written or online dispute form detailing the unauthorized transactions.
It is important to submit disputes promptly, as federal protections under the Electronic Fund Transfer Act (EFTA) require notification within 60 days of the statement showing the fraudulent charge for full liability protection.
During the dispute process, the bank will investigate and may temporarily credit the disputed amount. The cardholder should monitor account activity closely and keep all correspondence related to the fraud.
Proper management of this step improves the chances of recovering lost funds and prevents future fraudulent activities.
How Fraudsters Bypass Security Measures
Fraudsters exploit several techniques to access and use debit card information without physically holding the card. These methods often target security gaps in PIN verification, card data storage, and online transaction processes.
PIN Bypass Techniques
A debit card typically requires a PIN to complete transactions at ATMs or in-store purchases. However, criminals can bypass this requirement through methods such as skimming and phishing. Skimming devices installed on card readers capture both card information and PINs when a user inserts their card and enters the code.
In some cases, attackers gain access to PINs by tricing victims into revealing them via fake calls or messages. PINless debit cards, which allow purchases without a code, also increase vulnerability, as fraudsters only need the card number and sometimes the CVV to complete transactions.
Cloning and Card Duplication
Card cloning involves copying data from the magnetic stripe or chip to create a duplicate debit card. Hackers use skimming devices or malware to harvest the card’s magnetic stripe data, then encode it onto a blank card.
This cloned card works in physical stores or ATMs requiring a PIN unless additional safeguards like chip technology or two-factor authentication are in place. However, hacked data can sometimes bypass even these measures if the chip data is copied or intercepted.
Using Card Information for Online Purchases
Online transactions require only card details such as the number, expiration date, and CVV, avoiding the need for a physical card or PIN. Fraudsters obtain this data through data breaches, phishing scams, or purchasing it on the dark web.
Because many online merchants do not require PINs or biometric verification, stolen card information alone is enough to make unauthorized purchases. This “card-not-present” fraud is a common strategy, especially when merchants lack strong anti-fraud controls. Users are urged to monitor accounts closely and use secure payment methods when available.
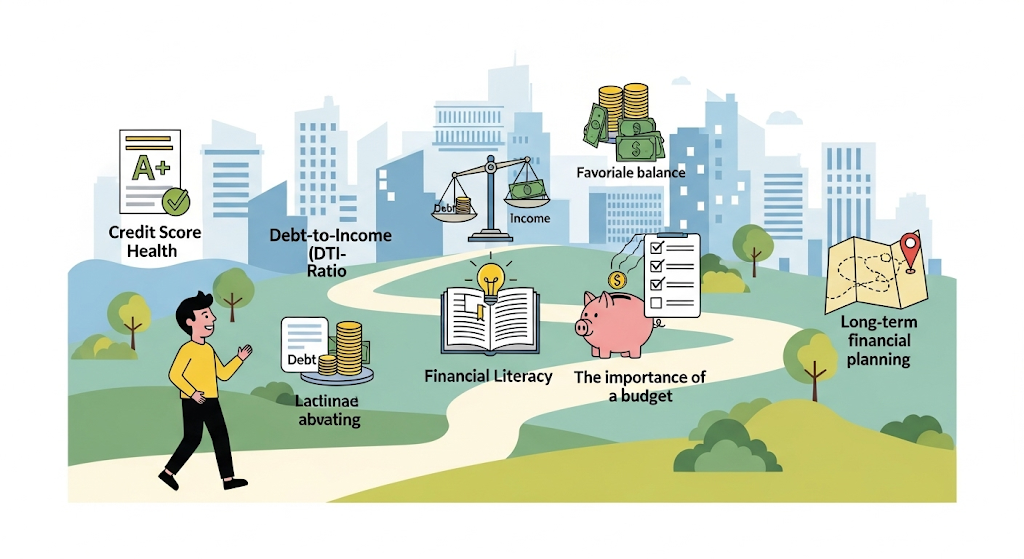
Preventing Future Debit Card Fraud
Preventing debit card fraud involves active steps to secure card information and detect unauthorized activity early. Practical actions like reviewing account activity, setting up real-time alerts, and adopting strong security habits reduce risk and limit potential losses.
Monitoring Accounts Regularly
Consistent account monitoring is crucial. Users should review bank statements and transaction histories daily or at least weekly to catch any unusual or unauthorized charges quickly.
Many banks, including those offering international debit cards like the Bank of Bhutan, provide detailed transaction records online. This makes it easier to identify suspicious activity, such as repeated small charges or transactions from unexpected locations.
If a transaction looks unfamiliar, customers should contact their bank immediately. Early detection can trigger faster fraud investigation and help protect available funds.
Using Account Alerts and Notifications
Setting up alerts is an effective layer of defense. Alerts can notify users via SMS or email when transactions exceed a certain amount or when purchases happen online or abroad.
Alerts help detect fraud even before it reflects on monthly statements. For example, the Bank of Bhutan’s international debit card allows customizing alert thresholds to stay informed about key transactions.
Customers should enable alerts for various activities, such as ATM withdrawals, large purchases, and potential security breaches. These real-time notifications provide timely awareness and can prevent further unauthorized use.
Following Card Security Best Practices
Applying proper security practices is essential to protect a debit card and associated account. Users should never share card details, PINs, or CVV numbers, especially online or over the phone.
Physical card security is important—keep the card in a safe place and avoid exposing it to others. Using strong, unique passwords for bank accounts and avoiding public Wi-Fi for online banking reduces hacking risks.
Furthermore, customers should be wary of phishing scams and only enter card information on secure websites (look for HTTPS). Regularly updating device security and software also minimizes vulnerabilities.
Using a debit card remains convenient when paired with vigilant habits and safety measures. Pros of debit cards like direct access to funds and wide acceptance can be fully enjoyed while minimizing exposure to fraud.
Legal Rights and Liability for Debit Card Fraud

Debit card fraud liability depends heavily on prompt reporting and understanding specific protections under federal law and bank policies. Cardholders must act quickly and be aware of how regulations limit their financial responsibility if unauthorized charges occur.
Reporting Timelines and Customer Responsibility
Federal law requires cardholders to report unauthorized debit card use quickly to limit their liability. If the fraud is reported within two business days of discovery, liability is capped at $50.
If the report comes after two days but within 60 days of the bank statement, the cardholder’s maximum loss rises to $500. Reporting beyond 60 days means potentially unlimited liability for charges.
Cardholders must review statements regularly and notify the bank immediately when suspicious activity is detected. Failure to act within these timeframes increases financial risk. Prompt reporting is essential to reduce losses.
Bank Policies on Fraudulent Charges
Banks typically have internal policies that align with federal laws but may offer additional protections. Many banks cover full losses if fraudulent activity is reported promptly and the customer followed security measures like protecting their PIN.
Using someone else’s debit card without permission can lead to serious legal consequences, including criminal charges and financial liability. An authorized user arrangement transfers account responsibility to the main cardholder.
Fraud investigations often require proof that the cardholder did not authorize or contribute to the transactions. Cooperation with bank procedures is necessary to resolve charges and recover funds.
Regulations and Consumer Protections
The Electronic Fund Transfer Act (EFTA) governs many aspects of debit card fraud protection. It limits liability and requires banks to investigate reported fraud promptly.
In Georgia, statute of limitations for credit card debt is typically six years, but first-time offenses related to card theft or credit card abuse may lead to misdemeanor or felony charges depending on the amount involved.
Felony-level credit card theft generally involves larger sums or repeated offenses and carries severe penalties, including potential imprisonment. Understanding these legal boundaries helps consumers navigate disputes and protect their rights.
Differentiating Debit Card Fraud From Credit Card Theft
Debit and credit card fraud involve unauthorized use, but they affect users differently in terms of liability, account impact, and resolution. Understanding these distinctions is crucial for managing risk and responding effectively if fraud occurs.
Liability Differences Between Debit and Credit Cards
Debit card users typically face more direct financial risk. Federal law limits liability to $50 if reported within two days, but beyond that, users could lose significantly more, including the full amount stolen. Some banks offer zero-liability protection, but policies vary widely.
Credit cards offer stronger built-in protections. The Fair Credit Billing Act limits consumer liability to $50, and many issuers waive this completely. This means fraud on credit cards generally results in less risk of immediate personal financial loss compared to debit cards.
For those with bad credit, debit cards may be easier to obtain, but this comes with greater responsibility to monitor transactions closely. Business credit cards from credit unions often provide enhanced fraud protection and dispute options, making them preferable for managing expenses securely.
Impact on Account Balances and Timelines
Debit card fraud removes funds directly from a checking account, potentially causing overdrafts or interrupted payments. Users might have to wait days or weeks for banks to investigate and restore stolen funds. This delay can affect bill payments and daily finances seriously.
Credit card fraud does not immediately impact bank balances. Unauthorized charges appear as pending transactions, allowing users to dispute them without affecting available cash. This delay in financial impact can reduce stress and provide time to identify unauthorized activity.
Anyone using debit cards should monitor transactions daily. Even if a card is inactive physically, digital theft can happen. Users of business credit cards benefit from detailed statements and alerts that help catch fraud quickly.
Fraud Resolution Process
Debit card fraud resolution often requires contacting the bank immediately. Banks may freeze the account, investigate the claim, and reimburse funds if fraud is confirmed. Users must provide documentation and answer questions, which can be time-consuming.
Credit card fraud claims typically follow a simpler process with faster resolution. Cardholders dispute invalid charges, and the issuer investigates while limiting financial responsibility for the user. The process protects credit standing and avoids draining personal funds.
Credit unions providing business credit cards tend to offer dedicated fraud support teams. This service can expedite resolution and provide customized advice for safeguarding accounts, particularly useful for small businesses and entrepreneurs managing multiple transactions.
Unusual and Related Debit Card Charges
Unrecognized charges often appear on statements as cryptic merchant names or unexpected amounts. Tracking down these charges requires careful review of transaction details and awareness of common billing practices that might seem suspicious but have legitimate origins.
Identifying Unknown Merchants and Charges
Many unknown charges occur because merchants use third-party payment processors or parent company names unfamiliar to cardholders. For example, a “Modern Leasing MI” charge might relate to a rental payment processed through a leasing company, even if the cardholder did not directly authorize it.
It’s important to cross-check merchant names with recent subscriptions, business transactions, or shared accounts. If a business debit card is used for personal purchases, unexpected fees may show up under less recognizable names like “JPMCB Card Services,” which refers to JP Morgan Chase billing or credit services linked to the card issuer.
Cardholders should list all known merchants and compare unfamiliar entries. They can contact the merchant or bank for clarification and potentially dispute unauthorized transactions that appear suspicious.
Decoding Transaction Descriptions
Transaction descriptions typically include a merchant name, location, or service type, but sometimes these details are abbreviated or coded. For instance, a charge might show only a payment processor’s name, complicating direct identification.
Understanding common abbreviations helps. “JPMCB” usually stands for JP Morgan Chase Bank, indicating a card service or fee. Charges appearing as cryptic codes often require contacting the card issuer for a clear explanation.
When deciphering transactions, note the date, amount, and any related purchase activity. Reviewing digital receipts or emails tied to the card helps confirm whether the charge matches a valid purchase or is fraudulent.
If charges are confusing, cardholders should use available banking app features or customer service to request additional transaction information or a merchant phone number.
| Common Abbreviations | Meaning |
|---|---|
| JPMCB | JP Morgan Chase Bank services |
| MI | Could indicate Michigan-based vendor or leasing fees |
| Leasing | Rental or lease-related payments |
Being methodical in reviewing transactions improves detection of fraudulent or accidental debits.
Connections to Broader Financial and Credit Issues
Unauthorized use of a debit card ties into wider financial concerns including the blurred lines with credit card fraud, implications for both business and personal accounts, and complications in resolving payment disputes. These factors affect how individuals protect their finances and pursue legal recourse when fraud occurs.
Relationship With Credit Card Fraud
Debit card fraud shares similarities with credit card fraud but differs significantly in risk exposure. Unlike credit card fraud, debit card fraud impacts funds directly from the cardholder’s bank account, often resulting in immediate loss of available cash.
Credit card companies tend to offer stronger protections and often do not hold customers responsible for unauthorized charges. Conversely, debit card fraud victims must act quickly to report the theft to minimize losses, as banks may delay refunds, impacting the victim’s liquidity.
Another difference lies in credit reporting. Credit card fraud can affect credit scores, while debit card fraud usually does not unless bank accounts become overdrawn and defaults occur. However, the recovery process in debit card cases can be more difficult when customers lack clear proof or documentation.
Business and Personal Debit Card Use
Businesses and individuals face different risks when using debit cards. Business accounts typically have larger transaction volumes, increasing exposure to fraud, especially in environments lacking robust security measures. For contractors, for example, unpaid invoices may lead to financial stress, and if there is no contract, suing for non-payment complicates matters further.
Personal debit card misuse can destabilize household finances immediately. Unlike credit cards, debit cards do not build credit history, so frequent fraudulent charges may not reflect on credit reports but can reduce cash flow needed for essentials.
Ensuring proper use of separate cards for business and personal accounts is essential. Businesses must keep comprehensive records to manage chargebacks and disputes, while individuals should monitor statements regularly for suspicious activity.
Payment Disputes and Legal Considerations
Disputing unauthorized debit card transactions often involves filing claims with the bank and sometimes legal action. Unlike credit cards, where cardholders have more leverage, debit card users may face longer wait times and more requirements to prove fraud.
Legal questions also arise around fees and recovery. For instance, whether an attorney can charge the client’s credit card transaction fee legally varies by jurisdiction and agreement terms.
The issue of liens is more relevant to credit cards. Credit card companies can place liens on a house following unresolved debt, but debit card misuse generally does not lead to liens because it affects cash balances rather than credit obligations.
For contractors without contracts, pursuing unpaid debts may require small claims court, where proof of payment or services is crucial. Payment disputes linked to debit card fraud complicate evidentiary needs and timely recovery of funds.